In today’s digital age, customer relationship management (CRM) software has become an essential tool for businesses across a wide range of industries. However, for life sciences and healthcare companies, whose clients are often medical practices, there is an added layer of complexity when it comes to implementing and using useful CRM software.
To benefit from the automation, workflow, and lead management features that CRM systems deliver, healthcare companies must ensure that their CRM solution is HIPAA compliant. In order for CRM software to meet HIPAA requirements, it must provide a secure platform for storing and managing any patient information that companies serving the healthcare industry may handle, ensuring that all data is kept confidential and secure.
For many businesses looking to provide services in the healthcare industry, HIPAA compliance, therefore, requires the implementation of various tools and controls. Meeting the strict protocols and requirements of the HIPAA compliance checklist makes many business leaders reluctant to take this challenge on. The result is that healthcare companies and healthcare providers have limited options when seeking healthcare software solutions for work management such as CRM (customer relationship management) and ERP (enterprise resource planning). But the right healthcare CRM can change this.
While at first glance HIPAA compliance may seem like an arduous undertaking, for many businesses, the security measures needed to be HIPAA compliant are already in place — and if they are not, they should be. Achieving and maintaining HIPAA compliance can ensure your customer information is safe and accessible and provide you with differentiation in a competitive business market.
This guide will outline the essential things you need to do to achieve and maintain HIPAA compliance with your CRM software.
What is CRM?
Before we dive into the details of why you need a HIPAA-compliant CRM platform, it’s important to first understand the benefits of the CRM software itself.
A CRM system provides a centralized database that stores all customer data, including contact information, purchase history, and interactions. This gives companies a complete view of each customer’s profile and their relationship with the company. Beyond this core offering, CRMs also deliver:
- Marketing automation: CRM systems automate marketing tasks such as email campaigns, social media posts, and lead scoring. This enables businesses to save time and increase efficiency. Marketing campaigns are streamlined and efficient, which also results in better customer engagement.
- Sales management: A CRM system helps businesses manage their sales pipeline more effectively. It does this by tracking leads, identifying sales opportunities, and monitoring sales performance.
- Improved customer communication: A CRM system enables businesses to communicate with customers more effectively through various channels. For example, email, phone, and social media. It also allows for personalized communication, which enhances customer engagement and satisfaction.
- Lead management: This involves qualifying and nurturing leads, and turning them into customers. Within the healthcare industry, lead management may refer to patient acquisition and patient engagement. CRMs enable easy management of this process.
- Customer analytics: A CRM system provides businesses with insights into customer behavior, preferences, and needs. This information can be used to optimize marketing and sales strategies and improve customer engagement and retention.
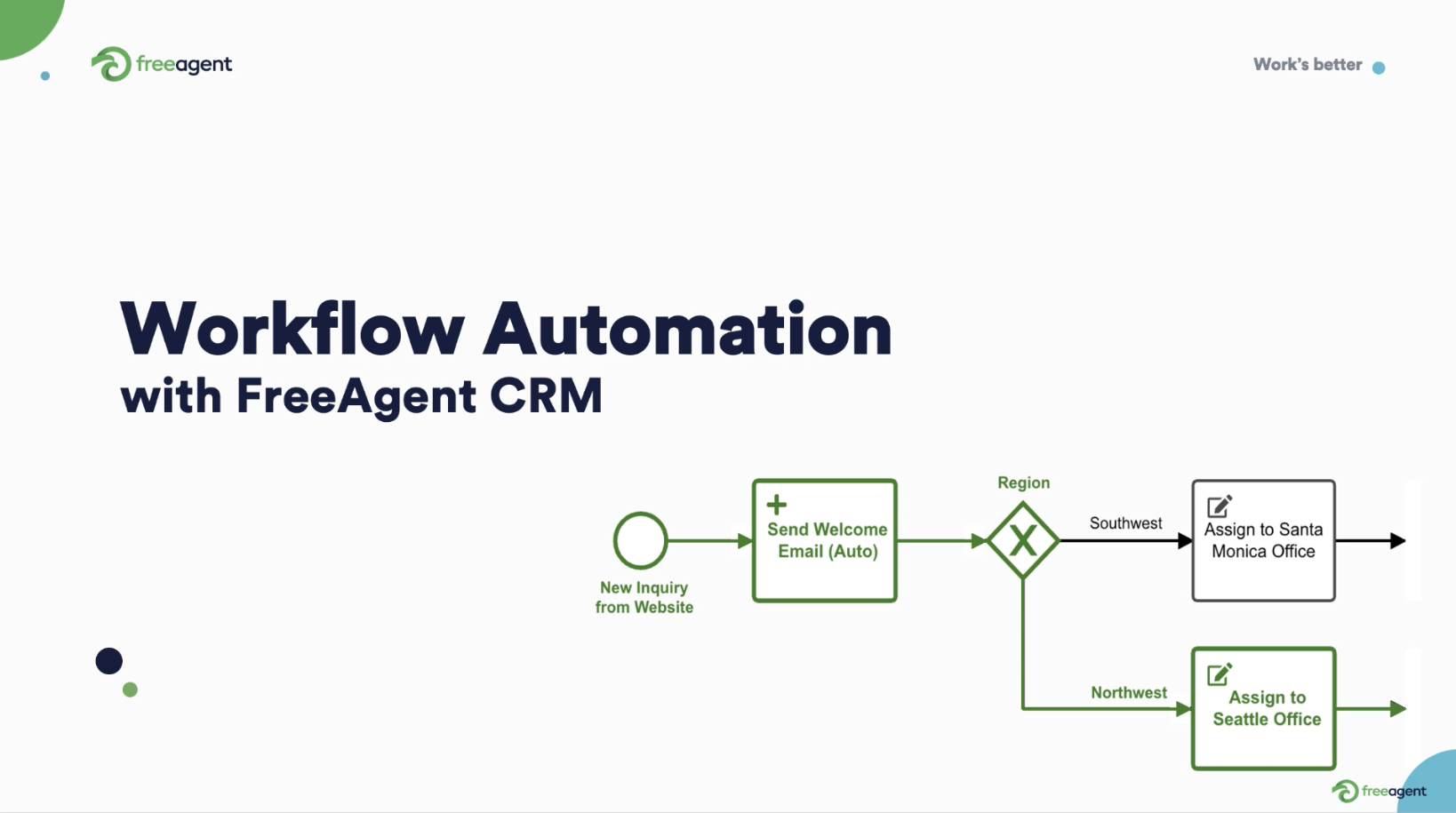
- Collaboration and workflow management: A CRM system improves collaboration among teams by providing a platform for sharing customer data and information. It also enables workflow automation, task assignment, and progress tracking.
- Customization and scalability: A CRM system can be customized to meet the specific needs of a business and can be scaled up or down as the business grows or changes. It can also be accessed through a desktop or mobile app for optimal efficiency.
Overall, a CRM system provides businesses with a powerful tool to manage their customer relationships, improve communication, and enhance customer satisfaction and loyalty.


What is HIPAA?
HIPAA (Health Insurance Portability and Accountability Act) is a set of standards that governs the collection, storage, and accessibility of private citizens’ healthcare information in the United States.
This covers sensitive patient information such as their electronic medical records (EMR), patient records, and more. HIPAA also ensures that a key element of practice management is centered around security features to keep this information safe. This applies across the whole customer journey, from when potential patients first enquire through to receiving care.
Any company or business that handles or processes the private health data of US citizens must adhere to these standards. While HIPAA is often thought of as a list of security protocols, its aim is to provide a better experience for patients navigating the complex world of healthcare services. Security is paramount, but every HIPAA regulation and HIPAA requirement considers accessibility and reliability as guiding principles as well.
The 3 rules of HIPAA
- The HIPAA Privacy Rule – These HIPAA compliance requirements restrict how patient information is shared. For example, the HIPAA Privacy Rule:
- Defines patient consent and how to obtain it
- Establishes rules for the rights of relatives and legal representatives
- Prevents the sharing of health information that can identify a patient
This HIPAA rule also outlines:
- What constitutes PHI (protected health information)
- How PHI can be shared
- A patient’s rights regarding their PHI
- Which organizations are required to comply with HIPAA
- The HIPAA Security Rule – These HIPAA compliance requirements govern the handling and protection of electronic health information (ePHI) using a combination of:
- Technical safeguards such as encryption and backups
- Administrative safeguards such as role-based access controls
- Physical safeguards such as keycard access to rooms and facilities where ePHI is stored
- The guidelines in the HIPAA Privacy Rule regarding PHI also apply to ePHI. The HIPAA Security Rule is an added layer to these requirements.
- The HIPAA Breach Notification Rule – The HIPAA Breach Notification Rule dictates what actions must be taken in the event of a security breach. For example, an information leak, electronic attack, or theft.
- In general, companies have 60 days to report a security breach to the authorities (US Department of Health and Human Services) and to the involved parties in cases where a person’s information has been compromised.
- For large-scale breaches, other protocols may be required as well. These may include informing the media in the local area.


Key elements of HIPAA compliance software
- Access controls: Access to ePHI must be strictly controlled at all times. For example, role-based access ensures only authorized individuals can access and view PHI. The system should also have user permissions to ensure that individuals can access only the information necessary for their job function. The software should allow administrators to set different levels of access for users based on their roles and responsibilities within the organization.
- The software should enable features such as:
- Unique user identifiers
- Multi-factor authentication
- Regular password changes
- Automatic logout parameters
Access control guidelines also include rules for handling the removal of access for former employees, providing authorization for new employees, and sharing information internally (both electronically and in person). - Encryption: All ePHI stored within a database must be encrypted. This is often referred to as at-rest encryption. Additionally, all ePHI must be encrypted before being transmitted and shared. This is often referred to as in-transit encryption.
- Backups: To prevent the loss of sensitive data, automatic, encrypted backups are required.
- Monitoring: Anytime ePHI is accessed or altered, it needs to be captured in a system log with details that include:
- The time of access
- The unique identifier of the person accessing or altering the information
- The type of information altered
- Storage: HIPAA also provides guidelines for the physical storage of ePHI, including the requirement that all ePHI for US citizens is stored in the US. Providers of HIPAA compliance software should also consider the HIPAA requirement that all of records captured in the system log are stored and accessible for six years.
- Data backup and recovery: The system should have backup and recovery procedures in place to ensure that data is not lost in case of system failure or disaster.
- HIPAA-compliant Business Associate Agreement (BAA): The CRM system vendor should sign a BAA with the healthcare provider or covered entity to ensure that they comply with HIPAA regulations and protect PHI.
- Customizable dashboards and reports: Customizable dashboards and reports help healthcare providers track patient data and outcomes.
- User-friendly interface: The CRM system should have an easy-to-use interface that is intuitive for healthcare providers and staff to use.
- Mobile compatibility: The system should be compatible with mobile devices to enable healthcare providers to access patient data remotely.
- Integration with other healthcare systems: The system should be able to integrate with other healthcare systems, such as EHRs (electronic health records), to streamline patient care and improve outcomes.
HIPAA compliance verification
There is no government certification for HIPAA compliance. Instead, healthcare organizations rely upon third-party assessors to determine a company’s compliance with HIPAA guidelines.
These assessors perform internal audits of a company’s processes and CRM platform and create a compliance plan to help that company maintain HIPAA standards. These third-party assessors can train employees, implement tools and systems, and tailor solutions to a company’s unique needs.
When a company demonstrates to the assessor that its processes are in accordance with HIPAA law, they are awarded a certificate, badge, or seal. While these verification awards are not recognized by the US Department of Health and Human Services, they are recognized by most organizations within the healthcare space. They are generally accepted as good faith proof of HIPAA compliance.

FreeAgent can help you maintain HIPAA compliance
FreeAgent is HIPAA-compliant healthcare CRM software and maintains HIPAA compliance through a number of specific practices and measures for small businesses and large businesses, including:
- Business Associate Agreements (BAA)- FreeAgent will enter into a BAA with any eligible organization.
- In-transit data encryption – We use secure TLS 1.2/1.3 protocols to encrypt all inbound and outbound communication outside our private data network.
- At-rest data encryption – We ensure physical access to disk storage is completely secure. To do this, we use Amazon Web Services (AWS) Key Management Service (KMS) technology with periodically rotated keys to encrypt all data on servers in our private network.
- ePHI (Electronic protected health information) – At FreeAgent, we secure all data with robust access controls. This includes role-based access controls (RBAC), multi-factor authentication (MFA), and periodic access reviews.
- Backups – We use automatic backups to ensure the ongoing availability and security of all data and systems.
- System logs – We store access logs and event logs to track all login attempts and changes made to data.
- HIPAA security personnel – We have designated HIPAA security personnel to implement policies and procedures to prevent, detect, contain, and correct breaches of ePHI.
HIPAA-compliant CRM software is a must-have for life sciences and pharmaceutical companies that handle sensitive patient data. By choosing a software solution that meets HIPAA requirements and has the features outlined above, organizations can ensure that they are protecting patient privacy and data while also streamlining their customer relationship management processes.
FreeAgent delivers HIPAA compliance and more
Our platform is designed to meet the unique needs of life sciences and healthcare companies that work with healthcare providers and need to maintain the privacy and security of patient data. But we also deliver a fully-fledged CRM software solution. Give your customer support and call center team a boost with our most popular features:
- HIPAA compliance: FreeAgent is fully compliant with HIPAA regulations, so you can rest assured that your patient data is secure and protected. If you’re providing services to healthcare clients, you are HIPAA compliant for online scheduling, appointment scheduling, management of medical records, appointment reminders, and more.
- Customizable forms and workflows: FreeAgent allows you to create customizable forms and workflows from templates to fit your specific needs.
- Automated reminders: FreeAgent’s automated reminder system helps you stay on top of your leads and follow-ups, resulting in better retention. Whether you get in touch by SMS or email, we have you covered.
- Secure messaging: FreeAgent includes a secure real-time messaging feature that allows you to communicate with patients and other healthcare providers securely and easily.
- Data analytics: FreeAgent includes powerful data analytics tools that help you analyze patient data and identify trends, making it easier to improve patient outcomes.
- User-friendly interface: FreeAgent’s user-friendly interface makes it easy to navigate and use the platform, even for non-technical users, supported by competitive pricing.
With FreeAgent, you can manage your leads across healthcare businesses with confidence, helping them with new patients and all aspects of telehealth, home health, and beyond. Operate securely knowing that key information is secure and your business is HIPAA compliant.
Try FreeAgent today and see how it can help streamline your practice workflows and improve patient care. Along with fellow market leaders like NexHealth, PatientPop, Caspio and Salesforce Health Cloud, we deliver HIPAA compliance. Unlike these other companies, FreeAgent also delivers so much more.
FreeAgent is leading the way to a better workday in healthcare and life sciences by providing flexible and adaptable enterprise tools that healthcare organizations can trust.
To see FreeAgent in action, get a demo, and discover for yourself how we are leading the way to a better workday.